INTRODUCTION
https://www.eff.org/issues/privacy
New technologies are radically advancing our freedoms, but
they are also enabling unparalleled invasions of privacy.
National and international laws have yet to catch up with
the evolving need for privacy that comes with new digital
technologies. Respect for individuals' autonomy, anonymous
speech, and the right to free association must be balanced
against legitimate concerns like law enforcement.
SMART DEVICES ARE SPYING ON YOU EVERYWHERE, AND THAT'S A PROBLEM
https://www.sciencealert.com/the-internet-of-things-is-probably-violating-your-privacy-here-s-how
HOW YOU ARE CONTINUOUSLY TRACKED VIA CELLULAR PHONES
Any turned on cellular phone continuously reports its
o EID (Embedded Identity Document) unique to eSIM card, or
o ICCID (Integrated Circuit Card Identifier) unique to a
physical SIM card, and
o IMEI (International Mobile Station Equipment Identity)
unique to physical device,
o and more.
HOW THE NSA THREATENS NATIONAL SECURITY
https://www.schneier.com/essays/archives/2014/01/how_the_nsa_threaten.html
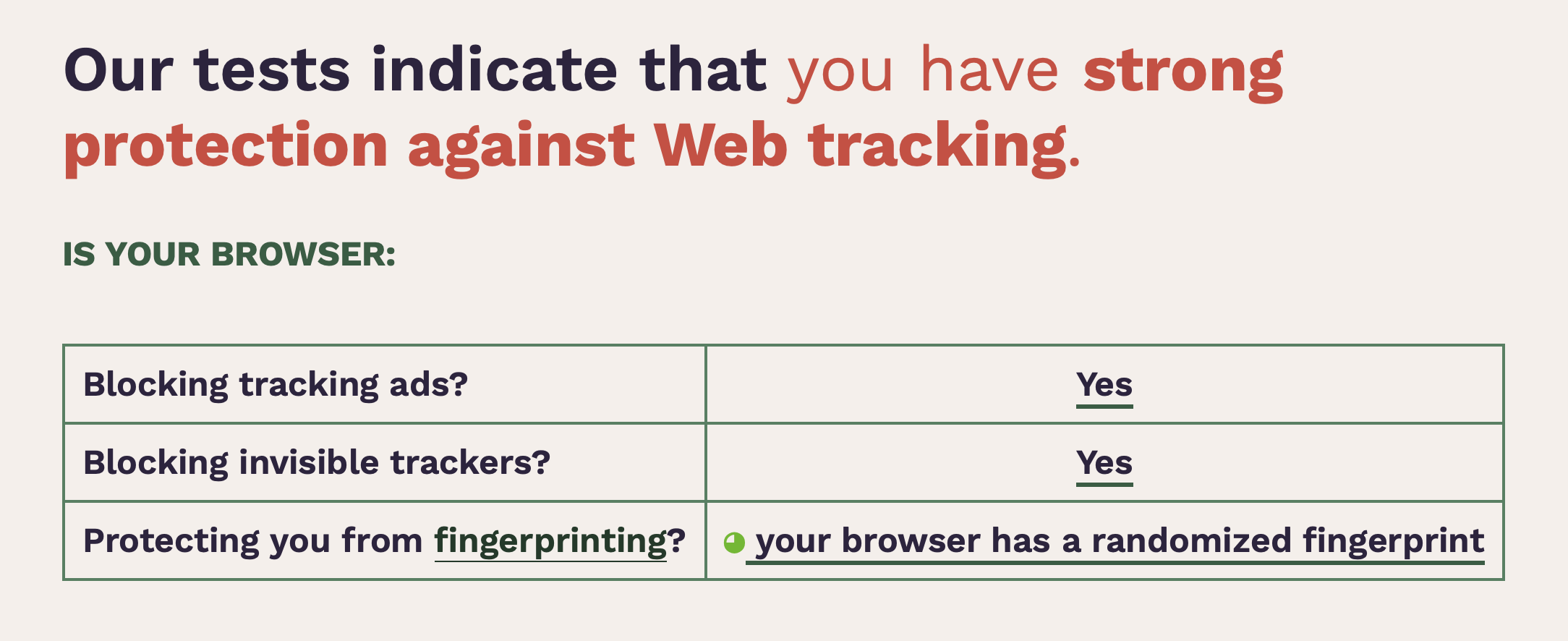
YOUR BROWSER (AND IP ADDRESS) CAN IDENTIFY YOU
Every device that connects to the internet, whether at home
or out and about, has an unique IP (Internet Protocol)
address. That address is known by your ISP (Internet Service
Provider) at home, your Cellular Carrier, and the providers
of WiFi networks you connect to in public.
See what your browser reveals every time you connect to a
website.
https://centralops.net/asp/co/BrowserMirror.vbs.asp
Browser Fingerprinting
https://coveryourtracks.eff.org/learn
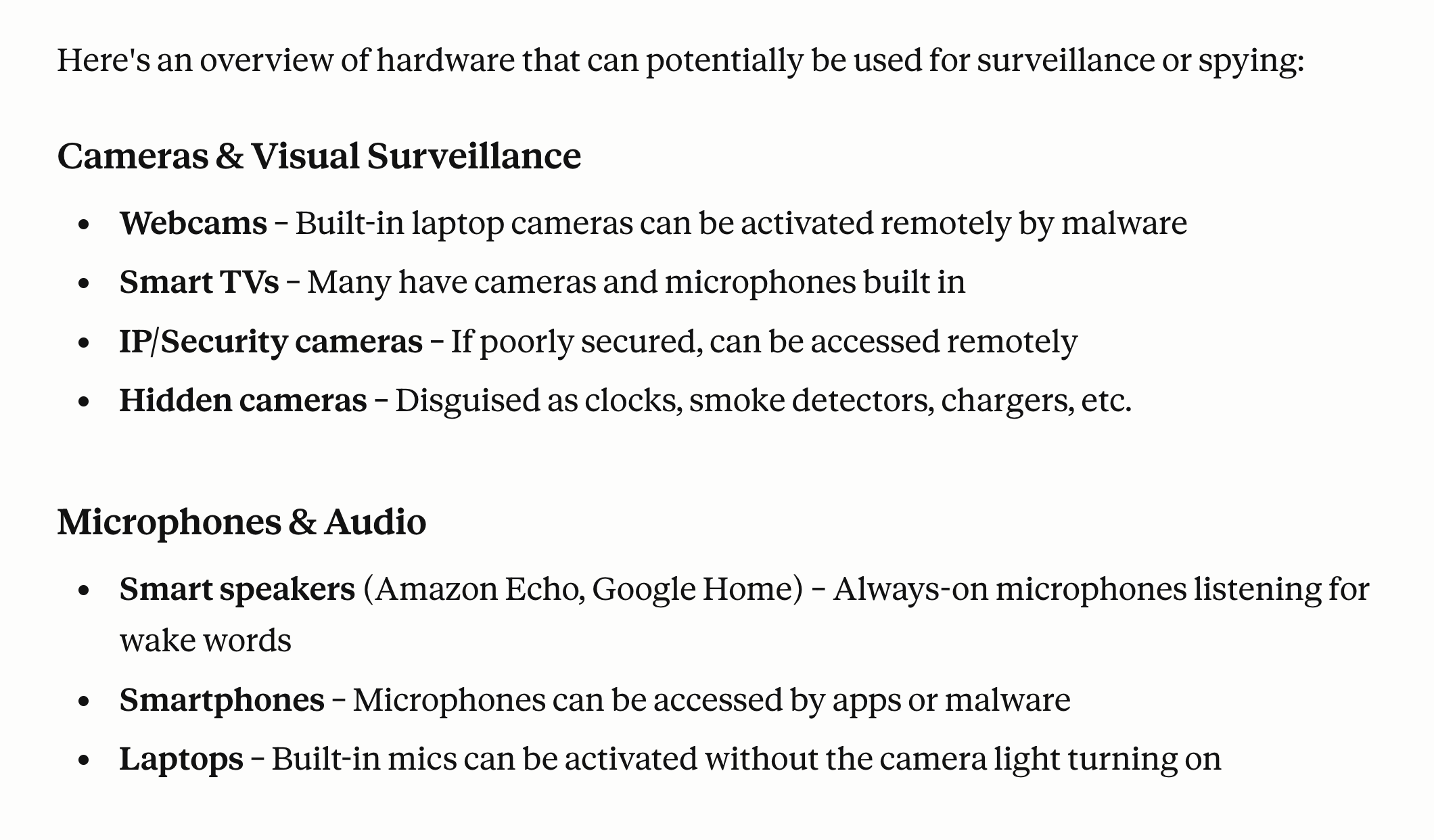
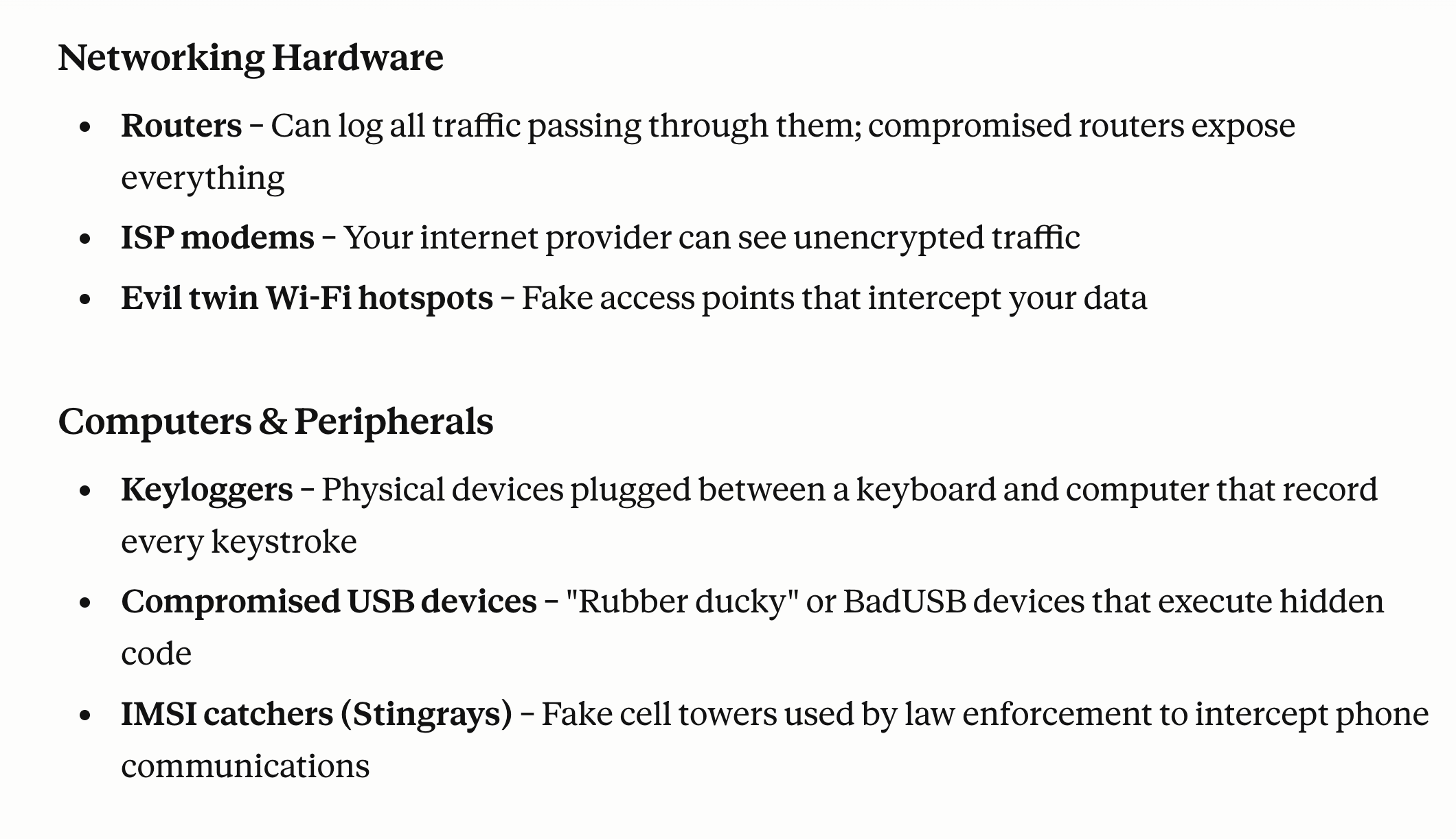
SPYING ON YOU
Major harvestors of information include: Google, Facebook,
Amazon, and the NSA. Most harvesting takes place by our
computers and mobile devices automatically running
JavaScript code embedded in websites we browse.
Things connected to the Internet (IoT). The Ring Doorbell
and many home security devices, meant to protect you, are
spying on you. Alexa, etc. is always listening to you.
How Your Phone is Tracked in 2026 Đ And How to Stop It
https://www.youtube.com/watch?v=amenY5QoWjM
Dangerous Apps - In the web of data brokers | DW Documentary
https://www.youtube.com/watch?v=Y07j3hXAI-g
Facebook's Extensive Surveillance Network
https://www.schneier.com/blog/archives/2024/02/facebooks-extensive-surveillance-network.html
Fifteen (15) Ways Google Collects Your Private Info and Data
https://www.quertime.com/article/15-ways-google-collects-your-private-info-and-data/
Four (4) ways Google is destroying privacy
https://www.salon.com/2014/02/05/4_ways_google_is_destroying_privacy_and_collecting_your_data_partner/
IF YOU CONTINUE TO USE GOOGLE, MANAGE YOUR GOOGLE ACCOUNT
https://myaccount.google.com/privacycheckup
https://myaccount.google.com/dashboard
https://myactivity.google.com
IT'S TIME TO DELETE THE SCARY AMOUNT OF DATA GOOGLE HAS ON YOU
https://www.cnet.com/tech/services-and-software/its-time-to-delete-the-scary-amount-of-data-google-has-on-you/
WHAT HARDWARE CAN SPY ON YOU?
DOCUMENTARIES & BOOK RECOMMEMDATIONS
GETTING HACKED (6+ min)
https://www.youtube.com/watch?v=fHhNWAKw0bY
The Social Dilemma (2020) | Netflix
https://www.imdb.com/title/tt11464826/?ref_=fn_al_tt_1
https://www.imdb.com/title/tt11464826/fullcredits/?ref_=tt_ql_cl
The Social Dilemma (2020) (55 min)
https://www.youtube.com/watch?v=iYVVgGWUKKg
Explores the dangerous human impact of social networking,
with tech experts sounding the alarm on their own
creations.
Web of Make Believe: Death, Lies and the Internet | Netflix Official Site
https://www.netflix.com/title/81122462 (Season 1, 6 episodes)
"It's Worse Than We Thought" | Edward Snowden (11+ min)
https://www.youtube.com/watch?v=TGzikHRumSY
Book: "Permanent Record" | Edward Snowden
https://www.amazon.com/Permanent-Record-Edward-Snowden/dp/1250237238
Edward Snowden, the man who risked everything to expose the
US government's system of mass surveillance, reveals for the
first time the story of his life, including how he helped to
build that system and what motivated him to try to bring it
down.
In 2013, twenty-nine-year-old Edward Snowden shocked the
world when he broke with the American intelligence
establishment and revealed that the United States government
was secretly pursuing the means to collect every single
phone call, text message, and email. The result would be an
unprecedented system of mass surveillance with the ability
to pry into the private lives of every person on earth. Six
years later, Snowden reveals for the very first time how he
helped to build this system and why he was moved to expose
it.
Spanning the bucolic Beltway suburbs of his childhood and
the clandestine CIA and NSA postings of his adulthood,
Permanent Record is the extraordinary account of a bright
young man who grew up online--a man who became a spy, a
whistleblower, and, in exile, the Internet's conscience.
Written with wit, grace, passion, and an unflinching candor,
Permanent Record is a crucial memoir of our digital
age and destined to be a classic.
Book: "The Snowden Files: The Inside Story of the World's
Most Wanted Man" by Luke Harding
https://www.amazon.com/Snowden-Files-Inside-Worlds-Wanted/dp/0804173524
Edward Snowden was a 29-year-old computer genius working for
the National Security Agency when he shocked the world by
exposing the near-universal mass surveillance programs of
the United States government. His whistleblowing has shaken
the leaders of nations worldwide, and generated a passionate
public debate on the dangers of global monitoring and the
threat to individual privacy.
In a tour de force of investigative journalism that reads
like a spy novel, award-winning Guardian reporter Luke
Harding tells Snowden's astonishing story-from the day he
left his glamorous girlfriend in Honolulu carrying a hard
drive full of secrets, to the weeks of his secret-spilling
in Hong Kong, to his battle for asylum and his exile in
Moscow. For the first time, Harding brings together the many
sources and strands of the story-touching on everything from
concerns about domestic spying to the complicity of the tech
sector-while also placing us in the room with Edward Snowden
himself. The result is a gripping insider narrative-and a
necessary and timely account of what is at stake for all of
us in the new digital age.
REGAINING SOME PRIVACY - WHAT CAN YOU DO?
USE A FARADAY BAGS (Two nested Faraday bags works better)
https://www.amazon.com/Faraday-Protector-Tuulin-Blocking-Blocker/dp/B07RSHRCSS
https://www.amazon.com/Mission-Darkness-Non-Window-Faraday-Phones/dp/B01A7MACL2
RF Signal Blocking - 100% shielding of WiFi (2.4GHz & 5GHz),
Bluetooth, cell signals including 5G networks, GPS, RFID,
and radio signals with 90dB average attenuation from low MHz
all the way up to 40GHz. EMI, RFI, EMF radiation shielding.
Airplane Mode will shut down cellular and bluetooth radios.
USE A VIRTUAL PRIVATE NETWORK (VPN)
http://edu-observatory.org/olli/Manage/VPN.html
Public networks such as WiFi at Universities, Airports,
Hotels, Doctor's offices, Hospitals, Libraries, Coffee
Shops, etc. ARE NOT SECURE. You have to assume there are bad
guys on those networks harvesting EVERYTHING you say, type
and read.
USE PUBLIC DNS SERVICE OPTIONS
http://edu-observatory.org/olli/Manage/DNS.html
Default DNS services are provided by your Internet Service
Provider (ISP) at home, your cellular provider, workplace,
and all public WiFi networks that you might use.
Many are logging everything you do. Some are blocking
websites. Your DNS history can identify you, perhaps even
better than tracking cookies.
SET A SECURE DEFAULT SEARCH ENGINE ON YOUR BROWSER
Switching to a more secure, privacy focused search engine is
another way to maintain better privacy while browsing the
web. Most of the popular search engines rely on selling
users advertisements to make money. Search engines like
Startpage, and DuckDuckGo are funded by donations and search
related advertising, not by harvesting and selling your
information.
DuckDuckGo does not track you
https://start.DuckDuckGo.com
Use Google without being tracked
https://www.startpage.com
HOW TO MANAGE COOKIES BY BROWSER
https://www.cookiepro.com/knowledge/how-to-manage-cookies-by-browser/
Almost all modern browsers provide mechanisms for users to
control how their computers handle cookies. This includes
the ability to block cookies and prevent them from being
loaded, as well as ways to delete the cookies already stored
on their device.
Website visitors are becoming more aware of the ways
advertisers track them across websites. To combat this
surveillance, popular web browsers are introducing new ways
to protect the privacy of their users. Google Chrome,
Safari, and Firefox have all announced big changes in 2020
that, when fully rolled out, should provide users with
increased protection from tracking technologies.
 REGULARLY DELETE HISTORY AND WEBSITE DATA (includes cookies)
Removing cookies and more. Wipe your computer of your
browsing history, cookies, and other detritus. It won't
solve the problem on its own, but it is almost essential to
clear away the tools people can use to track you.
WIPR 2 (designed for Apple devices)
https://apps.apple.com/us/app/wipr-2/id1662217862
Wipr 2 is an ad-blocking app designed for Apple devices,
including iPhones, iPads, and Macs. It aims to enhance your
browsing experience by blocking ads, trackers, and cookie
warnings.
Wipr 2 is praised for its effectiveness in filtering ads and
improving the overall browsing experience. Users report
significant reductions in visual clutter and faster loading
times on websites. The app updates its blocklist
automatically twice a week, ensuring it stays effective
against new ads and trackers.
ADGUARD (works on all computers and mobile devices)
https://adguard.com/en/adguard-browser-extension/overview.html
https://adguard.com/en/products.html
AdGuard is the fastest and most lightweight ad blocking
extension that effectively blocks all types of ads on all
web pages! Choose AdGuard for the browser you use and get
ad-free, fast and safe browsing.
PRIVACY BADGER (from the Electronic Frontier Foundation)
https://www.eff.org/privacybadger
https://www.eff.org/privacybadger/faq#Will-you-be-supporting-any-other-browsers-besides-Chrome-/-Firefox-/-Opera
https://ssd.eff.org/en/blog/privacy-badger-now-fights-more-sneaky-google-tracking
Privacy Badger is a browser add-on that stops advertisers
and other third-party trackers from secretly tracking where
you go and what pages you look at on the web. If an
advertiser seems to be tracking you across multiple websites
without your permission, Privacy Badger automatically blocks
that advertiser from loading any more content in your
browser. To the advertiser, it's like you suddenly
disappeared.
HUSH NAG BLOCKER
https://apps.apple.com/us/app/hush-nag-blocker/id1544743900
Browse the web like it should be - free of nags to accept
cookies or privacy invasive tracking. It's tiny, fast, free,
open, secure and without any access to your data.
APPLE ICLOUD PRIVATE RELAY
https://support.apple.com/en-us/HT212614
https://support.apple.com/guide/icloud/set-up-icloud-private-relay-mm7dc25cb68f/icloud
iCloud Private Relay is designed to protect your privacy by
ensuring that when you browse the web in Safari, no single
party - not even Apple - can see both who you are and what
sites you're visiting.
Testing Privacy
Web Browser Cookie Forensics
https://www.grc.com/cookies/forensics.htm
EFF -- Is your browser safe against tracking?
https://coveryourtracks.eff.org
REGULARLY DELETE HISTORY AND WEBSITE DATA (includes cookies)
Removing cookies and more. Wipe your computer of your
browsing history, cookies, and other detritus. It won't
solve the problem on its own, but it is almost essential to
clear away the tools people can use to track you.
WIPR 2 (designed for Apple devices)
https://apps.apple.com/us/app/wipr-2/id1662217862
Wipr 2 is an ad-blocking app designed for Apple devices,
including iPhones, iPads, and Macs. It aims to enhance your
browsing experience by blocking ads, trackers, and cookie
warnings.
Wipr 2 is praised for its effectiveness in filtering ads and
improving the overall browsing experience. Users report
significant reductions in visual clutter and faster loading
times on websites. The app updates its blocklist
automatically twice a week, ensuring it stays effective
against new ads and trackers.
ADGUARD (works on all computers and mobile devices)
https://adguard.com/en/adguard-browser-extension/overview.html
https://adguard.com/en/products.html
AdGuard is the fastest and most lightweight ad blocking
extension that effectively blocks all types of ads on all
web pages! Choose AdGuard for the browser you use and get
ad-free, fast and safe browsing.
PRIVACY BADGER (from the Electronic Frontier Foundation)
https://www.eff.org/privacybadger
https://www.eff.org/privacybadger/faq#Will-you-be-supporting-any-other-browsers-besides-Chrome-/-Firefox-/-Opera
https://ssd.eff.org/en/blog/privacy-badger-now-fights-more-sneaky-google-tracking
Privacy Badger is a browser add-on that stops advertisers
and other third-party trackers from secretly tracking where
you go and what pages you look at on the web. If an
advertiser seems to be tracking you across multiple websites
without your permission, Privacy Badger automatically blocks
that advertiser from loading any more content in your
browser. To the advertiser, it's like you suddenly
disappeared.
HUSH NAG BLOCKER
https://apps.apple.com/us/app/hush-nag-blocker/id1544743900
Browse the web like it should be - free of nags to accept
cookies or privacy invasive tracking. It's tiny, fast, free,
open, secure and without any access to your data.
APPLE ICLOUD PRIVATE RELAY
https://support.apple.com/en-us/HT212614
https://support.apple.com/guide/icloud/set-up-icloud-private-relay-mm7dc25cb68f/icloud
iCloud Private Relay is designed to protect your privacy by
ensuring that when you browse the web in Safari, no single
party - not even Apple - can see both who you are and what
sites you're visiting.
Testing Privacy
Web Browser Cookie Forensics
https://www.grc.com/cookies/forensics.htm
EFF -- Is your browser safe against tracking?
https://coveryourtracks.eff.org
 Browser Fingerprinting
https://pixelprivacy.com/resources/browser-fingerprinting/
SMARTPHONE APPS CAN AND DO SPY ON YOU
The apps in question are mostly games. They seem harmless,
but if you grant permission for those apps to use your
phone's microphone, they can listen to your life through the
phone-even when the app isn't being used.
Don't give apps permission to access location, microphone,
camera, contacts, files, network, photos, health data, etc.
unless absolutely necessary.
USE END-TO-END ENCRYPTION (E2EE)
https://en.wikipedia.org/wiki/End-to-end_encryption
http://edu-observatory.org/olli/Manage/E2EE.html
https://www.apple.com/newsroom/pdfs/The-Continued-Threat-to-Personal-Data-Key-Factors-Behind-the-2023-Increase.pdf
End-to-end encryption (E2EE) is a system of communication
where only the communicating users can read the messages. In
principle, it prevents potential eavesdroppers - including
telecom providers, Internet providers, and even the provider
of the communication service - from being able to access the
cryptographic keys needed to decrypt the conversation.
Apple iMessage And Facetime & Privacy
https://www.apple.com/legal/privacy/data/en/messages/
https://www.apple.com/legal/privacy/data/en/face-time/
We designed iMessage and FaceTime to use end-to-end
encryption, so there's no way for Apple to decrypt the
content of your conversations when they are in transit
between devices. Attachments you send over iMessage (such
as photos or videos) are encrypted so that no one but the
sender and receiver(s) can access them.
iMessage with PQ3: (Feb.21, 2024)
The new state of the art in quantum-secure messaging at scale
https://security.apple.com/blog/imessage-pq3/
Today we are announcing the most significant cryptographic
security upgrade in iMessage history with the introduction
of PQ3, a groundbreaking post-quantum cryptographic protocol
that advances the state of the art of end-to-end secure
messaging. With compromise-resilient encryption and
extensive defenses against even highly sophisticated quantum
attacks, PQ3 is the first messaging protocol to reach what
we call Level 3 security - providing protocol protections
that surpass those in all other widely deployed messaging
apps. To our knowledge, PQ3 has the strongest security
properties of any at-scale messaging protocol in the world.
Session - an end-to-end encrypted messenger that minimises
sensitive metadata
https://getsession.org
https://getsession.org/download
http://arxiv.org/pdf/2002.04609
https://apps.apple.com/us/app/session-private-messenger/id1470168868
Session is an end-to-end encrypted messenger that
minimises sensitive metadata, designed and built for
people who want absolute privacy and freedom from any form
of surveillance.
Signal - Secure Phone Calling & Text Messaging
https://www.signal.org
https://signalfoundation.org
https://www.signal.org/download/macos/
https://apps.apple.com/us/app/signal-private-messenger/id874139669
Signal messages and calls are always end-to-end encrypted
and painstakingly engineered to keep your communication
safe. We can't read your messages or see your calls, and
no one else can either.
OUTBOUND FIREWALLS on computers -- Monitor all web traffic
Best practices for configuring Windows Defender Firewall
https://docs.microsoft.com/en-us/windows/security/threat-protection/windows-firewall/best-practices-configuring
LuLu (Outbound Firewall for macOS) -- Patrick Wardle
https://objective-see.com/products/lulu.html
https://objective-see.com
SURVEILLANCE SELF-DEFENSE
https://ssd.eff.org
https://ssd.eff.org/module-categories/basics
https://ssd.eff.org/module-categories/tool-guides
PERSONAL SAFETY USER GUIDE
https://help.apple.com/pdf/personal-safety/en_US/personal-safety-user-guide.pdf
HUMAN BEHAVIOR
https://defensivecomputingchecklist.com
http://edu-observatory.org/olli/HCS/Week1.html
http://edu-observatory.org/olli/HCS/Week2.html
Browser Fingerprinting
https://pixelprivacy.com/resources/browser-fingerprinting/
SMARTPHONE APPS CAN AND DO SPY ON YOU
The apps in question are mostly games. They seem harmless,
but if you grant permission for those apps to use your
phone's microphone, they can listen to your life through the
phone-even when the app isn't being used.
Don't give apps permission to access location, microphone,
camera, contacts, files, network, photos, health data, etc.
unless absolutely necessary.
USE END-TO-END ENCRYPTION (E2EE)
https://en.wikipedia.org/wiki/End-to-end_encryption
http://edu-observatory.org/olli/Manage/E2EE.html
https://www.apple.com/newsroom/pdfs/The-Continued-Threat-to-Personal-Data-Key-Factors-Behind-the-2023-Increase.pdf
End-to-end encryption (E2EE) is a system of communication
where only the communicating users can read the messages. In
principle, it prevents potential eavesdroppers - including
telecom providers, Internet providers, and even the provider
of the communication service - from being able to access the
cryptographic keys needed to decrypt the conversation.
Apple iMessage And Facetime & Privacy
https://www.apple.com/legal/privacy/data/en/messages/
https://www.apple.com/legal/privacy/data/en/face-time/
We designed iMessage and FaceTime to use end-to-end
encryption, so there's no way for Apple to decrypt the
content of your conversations when they are in transit
between devices. Attachments you send over iMessage (such
as photos or videos) are encrypted so that no one but the
sender and receiver(s) can access them.
iMessage with PQ3: (Feb.21, 2024)
The new state of the art in quantum-secure messaging at scale
https://security.apple.com/blog/imessage-pq3/
Today we are announcing the most significant cryptographic
security upgrade in iMessage history with the introduction
of PQ3, a groundbreaking post-quantum cryptographic protocol
that advances the state of the art of end-to-end secure
messaging. With compromise-resilient encryption and
extensive defenses against even highly sophisticated quantum
attacks, PQ3 is the first messaging protocol to reach what
we call Level 3 security - providing protocol protections
that surpass those in all other widely deployed messaging
apps. To our knowledge, PQ3 has the strongest security
properties of any at-scale messaging protocol in the world.
Session - an end-to-end encrypted messenger that minimises
sensitive metadata
https://getsession.org
https://getsession.org/download
http://arxiv.org/pdf/2002.04609
https://apps.apple.com/us/app/session-private-messenger/id1470168868
Session is an end-to-end encrypted messenger that
minimises sensitive metadata, designed and built for
people who want absolute privacy and freedom from any form
of surveillance.
Signal - Secure Phone Calling & Text Messaging
https://www.signal.org
https://signalfoundation.org
https://www.signal.org/download/macos/
https://apps.apple.com/us/app/signal-private-messenger/id874139669
Signal messages and calls are always end-to-end encrypted
and painstakingly engineered to keep your communication
safe. We can't read your messages or see your calls, and
no one else can either.
OUTBOUND FIREWALLS on computers -- Monitor all web traffic
Best practices for configuring Windows Defender Firewall
https://docs.microsoft.com/en-us/windows/security/threat-protection/windows-firewall/best-practices-configuring
LuLu (Outbound Firewall for macOS) -- Patrick Wardle
https://objective-see.com/products/lulu.html
https://objective-see.com
SURVEILLANCE SELF-DEFENSE
https://ssd.eff.org
https://ssd.eff.org/module-categories/basics
https://ssd.eff.org/module-categories/tool-guides
PERSONAL SAFETY USER GUIDE
https://help.apple.com/pdf/personal-safety/en_US/personal-safety-user-guide.pdf
HUMAN BEHAVIOR
https://defensivecomputingchecklist.com
http://edu-observatory.org/olli/HCS/Week1.html
http://edu-observatory.org/olli/HCS/Week2.html
RESOURCES
ELECTRONIC FRONTIER FOUNDATION (EFF)
https://www.eff.org
https://ssd.eff.org/en/module/your-security-plan
APPLE'S APPROACH TO PRIVACY
https://www.apple.com/privacy/
https://www.apple.com/privacy/features/
https://www.apple.com/privacy/manage-your-privacy/
sam.wormley@icloud.com
REGULARLY DELETE HISTORY AND WEBSITE DATA (includes cookies) Removing cookies and more. Wipe your computer of your browsing history, cookies, and other detritus. It won't solve the problem on its own, but it is almost essential to clear away the tools people can use to track you. WIPR 2 (designed for Apple devices) https://apps.apple.com/us/app/wipr-2/id1662217862 Wipr 2 is an ad-blocking app designed for Apple devices, including iPhones, iPads, and Macs. It aims to enhance your browsing experience by blocking ads, trackers, and cookie warnings. Wipr 2 is praised for its effectiveness in filtering ads and improving the overall browsing experience. Users report significant reductions in visual clutter and faster loading times on websites. The app updates its blocklist automatically twice a week, ensuring it stays effective against new ads and trackers. ADGUARD (works on all computers and mobile devices) https://adguard.com/en/adguard-browser-extension/overview.html https://adguard.com/en/products.html AdGuard is the fastest and most lightweight ad blocking extension that effectively blocks all types of ads on all web pages! Choose AdGuard for the browser you use and get ad-free, fast and safe browsing. PRIVACY BADGER (from the Electronic Frontier Foundation) https://www.eff.org/privacybadger https://www.eff.org/privacybadger/faq#Will-you-be-supporting-any-other-browsers-besides-Chrome-/-Firefox-/-Opera https://ssd.eff.org/en/blog/privacy-badger-now-fights-more-sneaky-google-tracking Privacy Badger is a browser add-on that stops advertisers and other third-party trackers from secretly tracking where you go and what pages you look at on the web. If an advertiser seems to be tracking you across multiple websites without your permission, Privacy Badger automatically blocks that advertiser from loading any more content in your browser. To the advertiser, it's like you suddenly disappeared. HUSH NAG BLOCKER https://apps.apple.com/us/app/hush-nag-blocker/id1544743900 Browse the web like it should be - free of nags to accept cookies or privacy invasive tracking. It's tiny, fast, free, open, secure and without any access to your data. APPLE ICLOUD PRIVATE RELAY https://support.apple.com/en-us/HT212614 https://support.apple.com/guide/icloud/set-up-icloud-private-relay-mm7dc25cb68f/icloud iCloud Private Relay is designed to protect your privacy by ensuring that when you browse the web in Safari, no single party - not even Apple - can see both who you are and what sites you're visiting. Testing Privacy Web Browser Cookie Forensics https://www.grc.com/cookies/forensics.htm EFF -- Is your browser safe against tracking? https://coveryourtracks.eff.org
Browser Fingerprinting https://pixelprivacy.com/resources/browser-fingerprinting/ SMARTPHONE APPS CAN AND DO SPY ON YOU The apps in question are mostly games. They seem harmless, but if you grant permission for those apps to use your phone's microphone, they can listen to your life through the phone-even when the app isn't being used. Don't give apps permission to access location, microphone, camera, contacts, files, network, photos, health data, etc. unless absolutely necessary. USE END-TO-END ENCRYPTION (E2EE) https://en.wikipedia.org/wiki/End-to-end_encryption http://edu-observatory.org/olli/Manage/E2EE.html https://www.apple.com/newsroom/pdfs/The-Continued-Threat-to-Personal-Data-Key-Factors-Behind-the-2023-Increase.pdf End-to-end encryption (E2EE) is a system of communication where only the communicating users can read the messages. In principle, it prevents potential eavesdroppers - including telecom providers, Internet providers, and even the provider of the communication service - from being able to access the cryptographic keys needed to decrypt the conversation. Apple iMessage And Facetime & Privacy https://www.apple.com/legal/privacy/data/en/messages/ https://www.apple.com/legal/privacy/data/en/face-time/ We designed iMessage and FaceTime to use end-to-end encryption, so there's no way for Apple to decrypt the content of your conversations when they are in transit between devices. Attachments you send over iMessage (such as photos or videos) are encrypted so that no one but the sender and receiver(s) can access them. iMessage with PQ3: (Feb.21, 2024) The new state of the art in quantum-secure messaging at scale https://security.apple.com/blog/imessage-pq3/ Today we are announcing the most significant cryptographic security upgrade in iMessage history with the introduction of PQ3, a groundbreaking post-quantum cryptographic protocol that advances the state of the art of end-to-end secure messaging. With compromise-resilient encryption and extensive defenses against even highly sophisticated quantum attacks, PQ3 is the first messaging protocol to reach what we call Level 3 security - providing protocol protections that surpass those in all other widely deployed messaging apps. To our knowledge, PQ3 has the strongest security properties of any at-scale messaging protocol in the world. Session - an end-to-end encrypted messenger that minimises sensitive metadata https://getsession.org https://getsession.org/download http://arxiv.org/pdf/2002.04609 https://apps.apple.com/us/app/session-private-messenger/id1470168868 Session is an end-to-end encrypted messenger that minimises sensitive metadata, designed and built for people who want absolute privacy and freedom from any form of surveillance. Signal - Secure Phone Calling & Text Messaging https://www.signal.org https://signalfoundation.org https://www.signal.org/download/macos/ https://apps.apple.com/us/app/signal-private-messenger/id874139669 Signal messages and calls are always end-to-end encrypted and painstakingly engineered to keep your communication safe. We can't read your messages or see your calls, and no one else can either. OUTBOUND FIREWALLS on computers -- Monitor all web traffic Best practices for configuring Windows Defender Firewall https://docs.microsoft.com/en-us/windows/security/threat-protection/windows-firewall/best-practices-configuring LuLu (Outbound Firewall for macOS) -- Patrick Wardle https://objective-see.com/products/lulu.html https://objective-see.com SURVEILLANCE SELF-DEFENSE https://ssd.eff.org https://ssd.eff.org/module-categories/basics https://ssd.eff.org/module-categories/tool-guides PERSONAL SAFETY USER GUIDE https://help.apple.com/pdf/personal-safety/en_US/personal-safety-user-guide.pdf HUMAN BEHAVIOR https://defensivecomputingchecklist.com http://edu-observatory.org/olli/HCS/Week1.html http://edu-observatory.org/olli/HCS/Week2.html